News

News

Cybersecurity Market Update Q1 2026
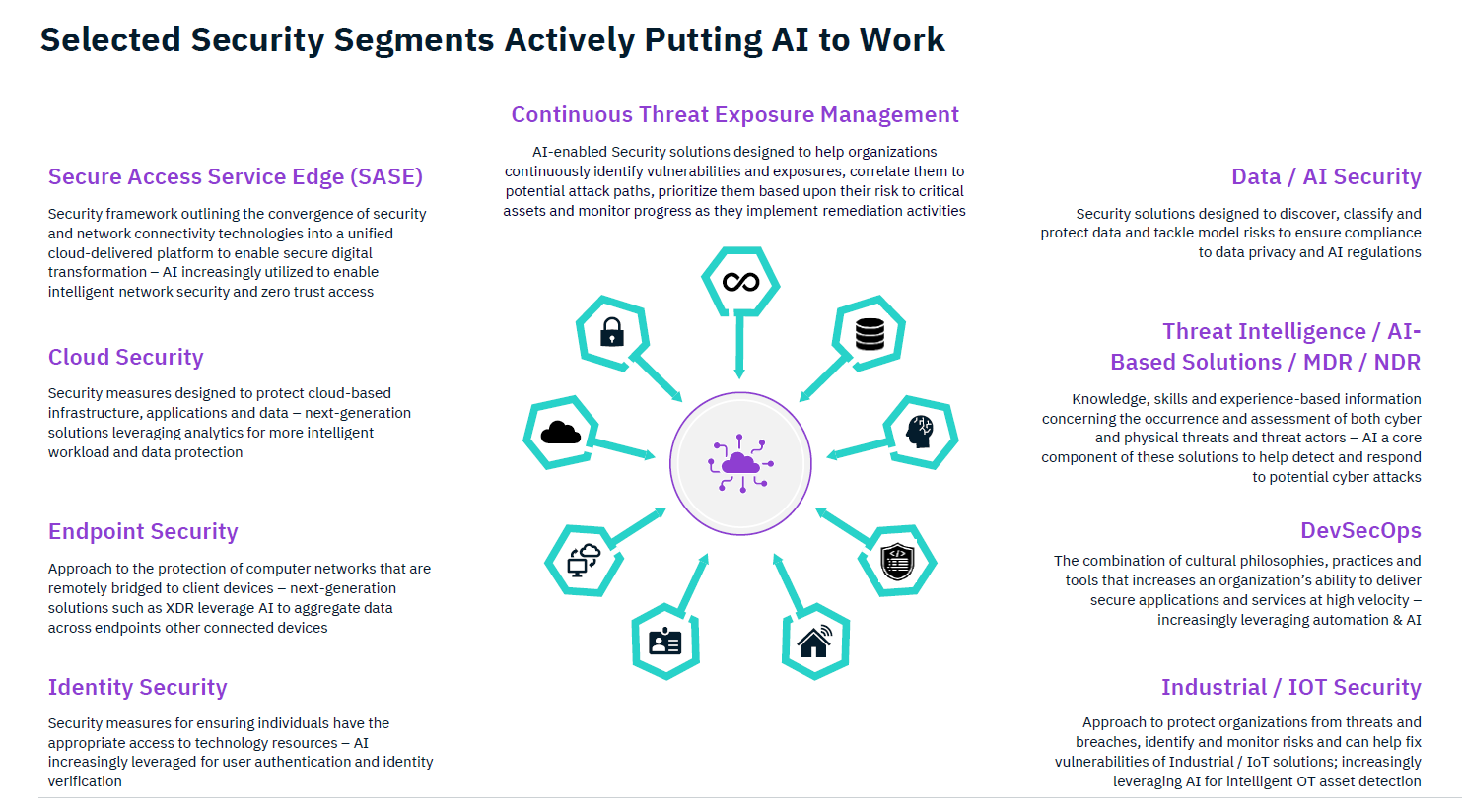
Bowen’s latest Cybersecurity Market Update examines the evolving threat landscape and highlights how established & emerging cybersecurity vendors are responding with new and innovative solutions. The presentation also features our latest cybersecurity market landscape and takes a deeper look at several key sub-sectors where we are seeing notable strategic activity, including Data & AI Security, Identity Security, Threat Intelligence, and Continuous Threat Exposure Management (CTEM).
Overview
- AI-powered cybersecurity attacks continue to grow in scale and complexity, raising fresh concerns about the ability of supply chain and ransomware threats to cause significant disruption across enterprise and critical infrastructure environments. While the industry has made meaningful strides in detection, response and resilience, the rapidly expanding threat landscape requires continued investment and innovation by the cyber ecosystem.
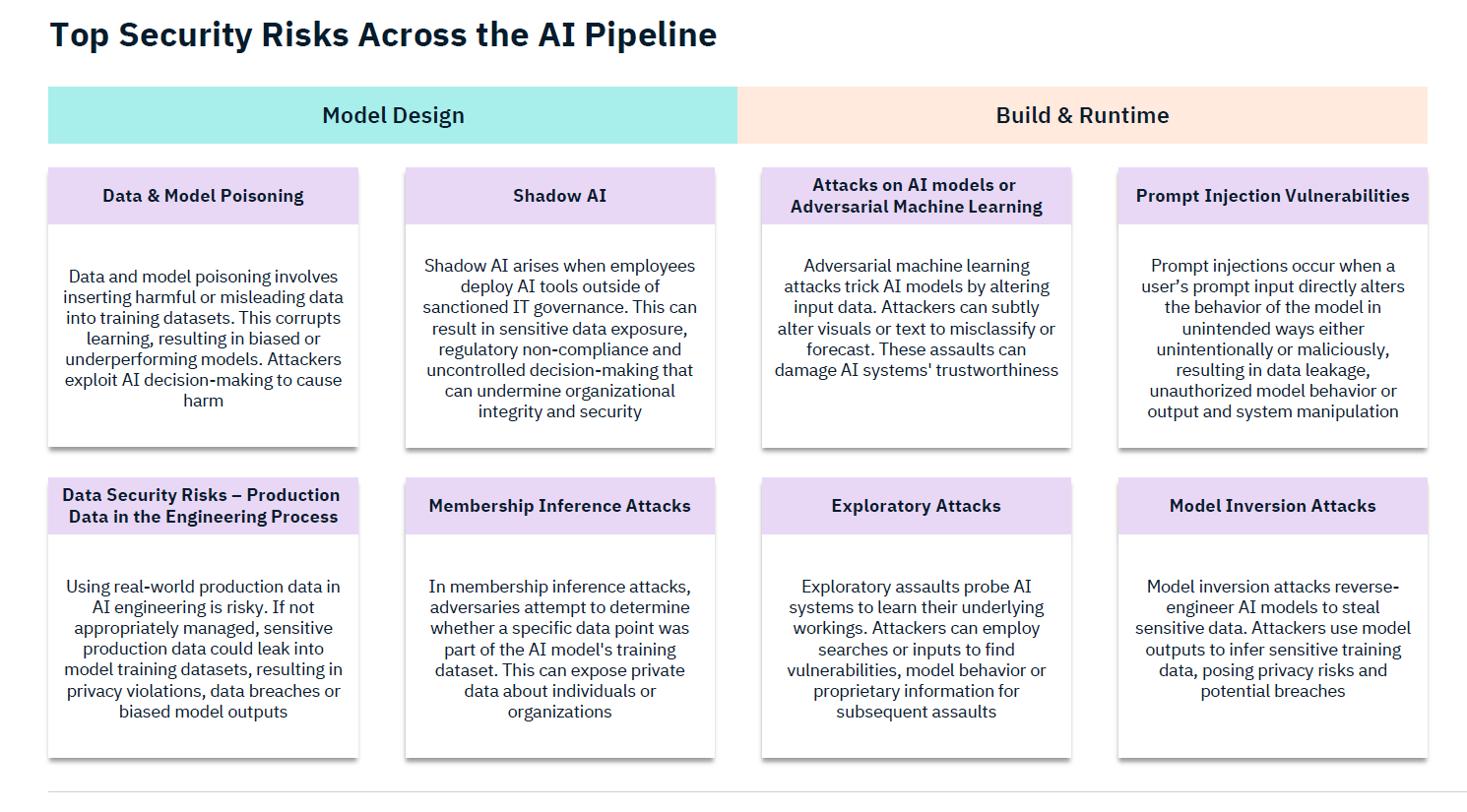
- As enterprises accelerate AI adoption, a new class of AI-specific threats including prompt injection, model poisoning and shadow AI are forcing organizations to secure the entire AI pipeline from design through deployment, fueling demand for capabilities such as AI firewalls, model scanning, AI red-teaming, runtime protection and AI guardrails.
- Stolen credentials and privilege escalation remain the leading entry points for ransomware attacks, and the rapid emergence of autonomous AI agents operating with persistent machine identities and minimal oversight is compounding this challenge. As a result, there is accelerating demand for identity security solutions that can enforce authentication, governance and real-time threat detection across an expanding universe of human and non-human identities.
- The limitations of legacy tools such as SIEM and signature-based detection have accelerated the shift toward AI-enhanced threat intelligence platforms that can autonomously monitor and respond to threats across an expanding range of data sources, freeing security operations teams to focus on high-value investigations rather than manual alert management.
- As digital transformation accelerates and attack surfaces expand at an unprecedented rate, traditional vulnerability management approaches that rely on point-in-time assessments are proving insufficient, driving adoption of the five-stage CTEM framework that continuously identifies, prioritizes and validates exposure across an organization’s entire ecosystem to enable faster and more efficient remediation.
The full report digs deeper into the Data & AI Security, Identity, Threat Intelligence, and CTEM sectors, highlighting Bowen credentials, industry trends, recent transactions, and key valuation multiples.
Download the report here.
Learn more about Bowen’s Cybersecurity Practice.




